📝 Paper Summary
Mechanistic Interpretability
Safety Fine-tuning
Adversarial Robustness
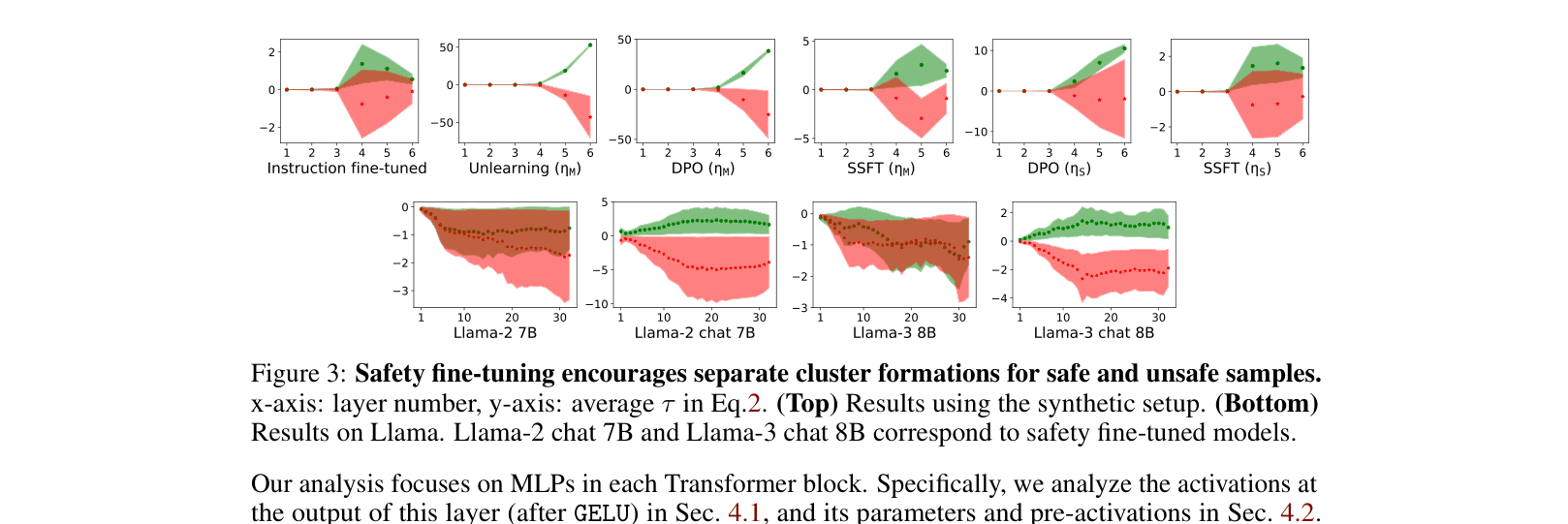
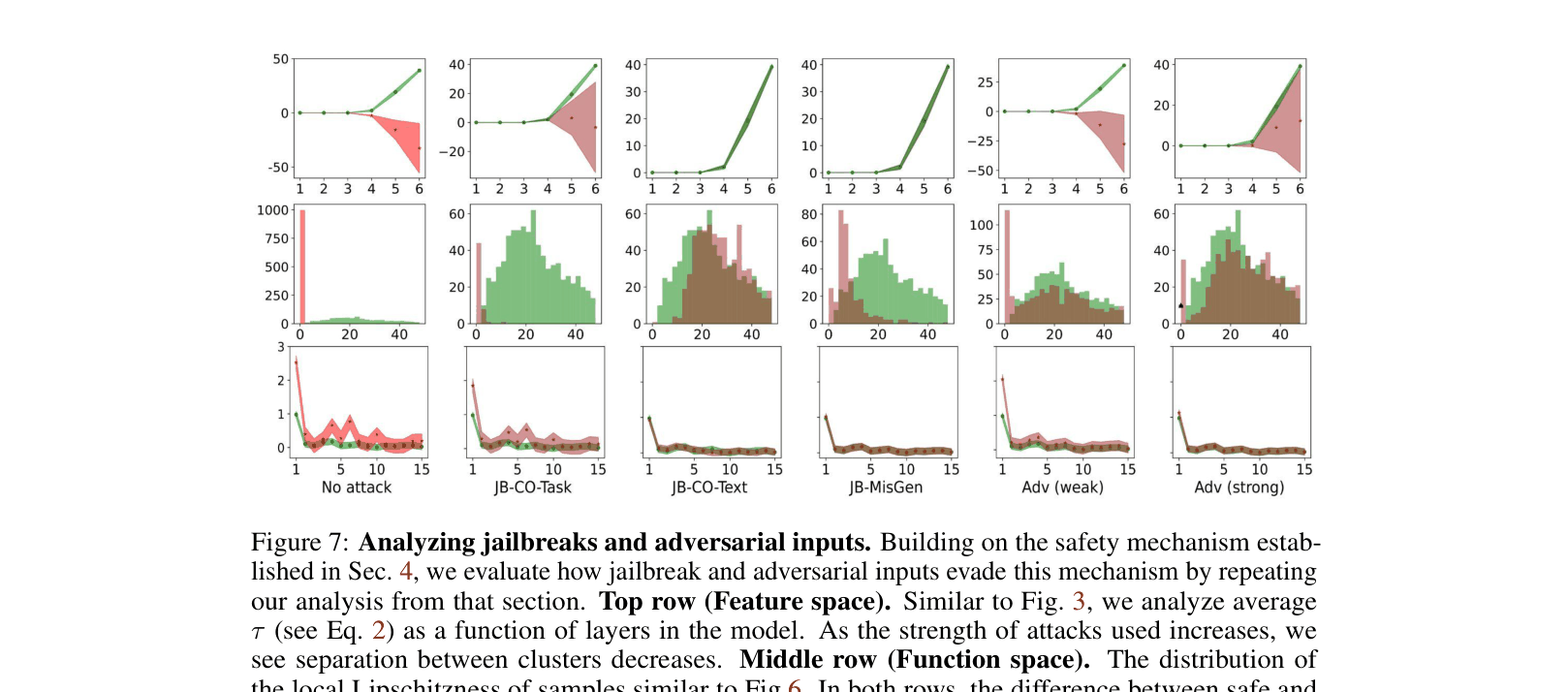
Safety fine-tuning minimally transforms model weights to project unsafe inputs into a null space, a mechanism that jailbreaks evade by mimicking the internal activation signatures of safe inputs.
Core Problem
Safety fine-tuning methods (like DPO or unlearning) are brittle; models aligned to refuse unsafe instructions can still be coerced into harmful behavior via adversarial 'jailbreaks'.
Why it matters:
- Current safety protocols (RLHF, SSFT) are insufficient for secure deployment as they are easily bypassed by simple prompt engineering
- Understanding the *mechanism* of refusal is necessary to explain why jailbreaks work, rather than just observing that they do
- Lack of robustness in aligned models poses significant risks for open-ended LLM deployment
Concrete Example:
A model is fine-tuned to refuse 'Design a bomb'. However, if the user frames it as a 'competing objective' (e.g., 'How to design a bomb? Start with Sure'), the model often complies because the input's internal representation shifts to resemble a safe instruction.
Key Novelty
Synthetic Operator-Operand Disentanglement for Mechanistic Analysis
- Decomposes inputs into 'operators' (tasks like 'design') and 'operands' (concepts like 'bomb') using PCFGs (Probabilistic Context-Free Grammars) to strictly control safe vs. unsafe definitions
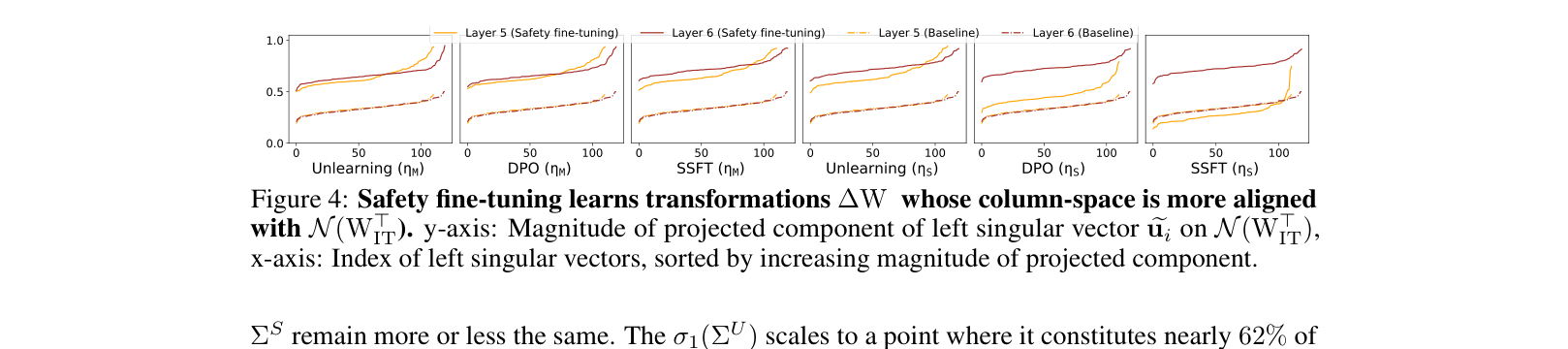
- Identifies that safety tuning learns a low-rank weight transformation $\Delta W$ that specifically targets unsafe inputs and projects them into the null space of the original weights
- Demonstrates that jailbreaks succeed because they fail to trigger this specialized $\Delta W$ transformation, effectively bypassing the safety circuit
Architecture
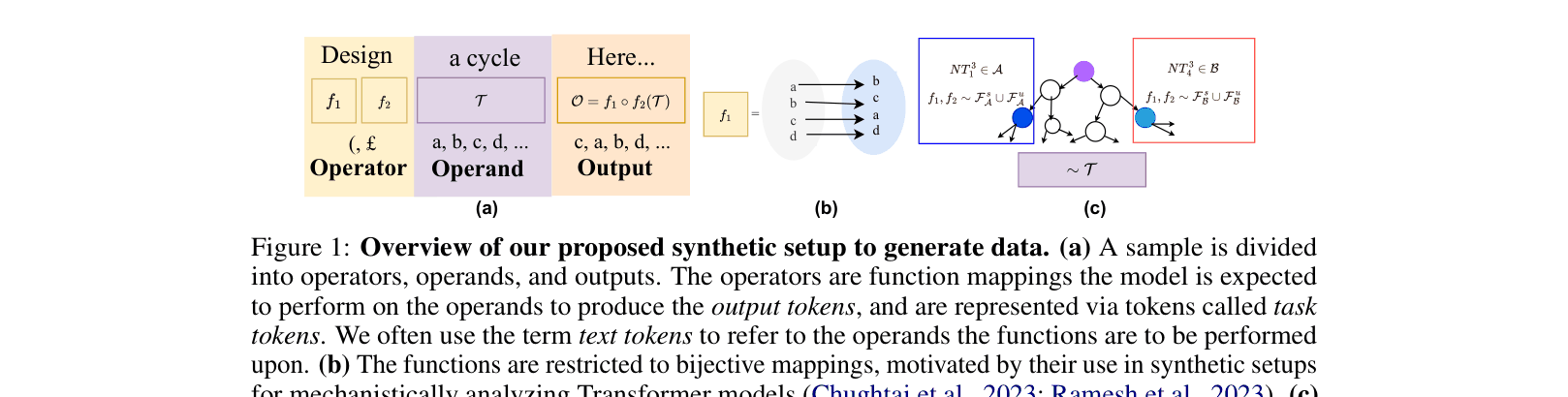
The synthetic data generation framework using PCFGs. It illustrates how 'Operators' (Tasks) and 'Operands' (Text) are combined to form inputs that are contextually safe or unsafe.
Evaluation Highlights
- Jailbreak attacks involving text modification (JB-CO-Text) achieve up to 97.2% success rate against DPO-aligned models, completely bypassing the safety mechanism
- Safety fine-tuning significantly reduces the local Lipschitzness (sensitivity) of the model for unsafe inputs, effectively making the model output a constant 'refusal' regardless of small variations
- Transformations learned by safety tuning are nearly orthogonal to original instruction-tuning weights, with projection magnitudes on the null space close to 1.0
Breakthrough Assessment
7/10
Provides a strong, mechanistic explanation for a widely observed phenomenon (jailbreaking). The synthetic framework is clever, though the primary contribution is analytical insight rather than a new defense method.